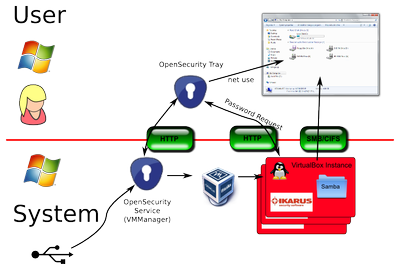
The Secure USB and Secure Web Browsing features have been integrated with an existing Windows-interface and with Windows user workflows. Data import and -export occur via the Windows Explorer. The Secure Browser opens as a window on the desktop and persists user bookmarks. In both mechanisms the user does not need to deal directly with the SecureVirtualMachine. If necessary the OpenSecurity user is being guided through any required steps by tray-notifications and dialogues.
OpenSecurity was tested under normal office conditions by the stakeholder IKT Linz. Additional requirements on the existing infrastructure could be modularly and flexibly implemented.
Secure USB
The current version of OpenSecurity allows data import from both unencrypted and encrypted USB-sticks. Imported data is automatically (and potentially centrally, if so configured) virus- and malware scanned. If a potential virus or malware is detected by the system, access to the data is denied. Potential viruses/rootkits that automatically activate upon access, can – if they are able to run on a Linux-system at all – only harm the used disposable SecureVirtualMachine, and not the user workstation.
It is also possible to export data to a USB-stick. In this case the user is requested to initialise the stick with an encrypted container. This way OpenSecurity prevents data loss by prohibiting export to devices other than encrypted USB-sticks.
In addition, it is possible for all data transactions to be recorded on a central logging- or monitoring server. In this way, potential data losses can be tracked.
Secure Web Browsing
By clicking the desktop- or tray-icon, the user can start the Secure Browser. In OpenSecurity Version 1.0 the open browser Chromium is being used. The browser is executed within a SecurityVirtualMachine, which is graphically integrated with the Windows-interface. It opens as a standard browser window in the usual desktop environment.
Also in this case a virus or malware attack originating from the browser can only affect the SecurityVirtualMachine and cannot contaminate the user workstation. Data from the browsing session can only be transferred via similar mechanisms and security measures as in the USB data import/export feature.